
BREAKING: Police Name Suspect in Alleged Savannah Guthrie Family Ransom Plot — Investigation Enters Critical Phase*
Authorities have identified a suspect in what officials describe as an alleged ransom plot connected to the family of television journalist Savannah Guthrie, according to law enforcement sources familiar with the developing investigation. While many details remain sealed, investigators say the case has moved into a new and highly sensitive stage.

Police emphasized that the suspect has been identified but not yet convicted, and the allegations remain under active investigation. Officials cautioned the public against speculation as detectives continue gathering evidence.
The case first came to light earlier this week when authorities confirmed they were examining a “credible threat” involving an attempt to demand money in exchange for the safety of a family member. Law enforcement sources described the communication as targeted and deliberate, prompting immediate coordination between local police and federal agencies.
“This was not treated as a routine threat,” one senior official said during a brief press conference. “Given the nature of the allegation and the individuals involved, we acted swiftly to ensure safety and preserve evidence.”
According to investigators, the suspect was identified after a digital trail allegedly connected electronic communications to a specific individual. Authorities have not publicly released the suspect’s name, citing ongoing legal procedures and the need to protect the integrity of the case.
The alleged ransom communication reportedly included detailed instructions and references that suggested familiarity with the family’s routines. That element has intensified scrutiny, as investigators work to determine whether the suspect acted alone or had access to insider information.
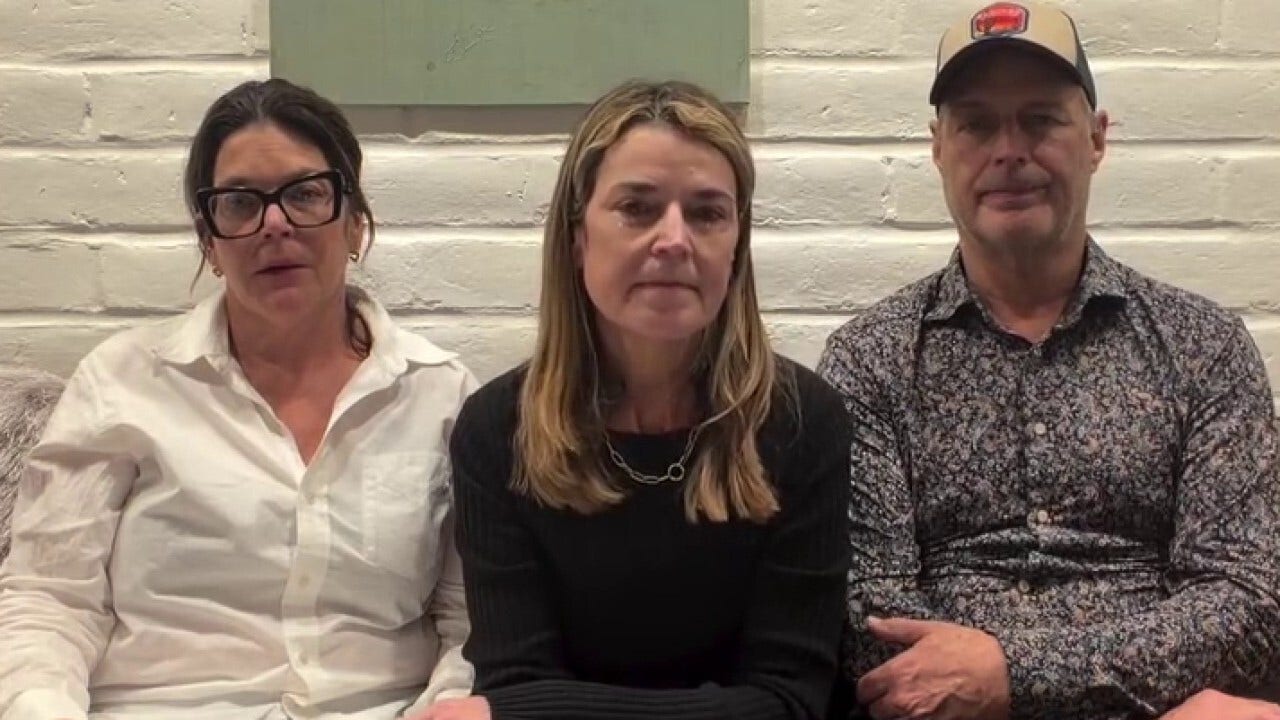
Savannah Guthrie, a prominent broadcast journalist known for her work in national news, has not issued a personal statement beyond thanking law enforcement for their rapid response. A spokesperson for her family said they are “cooperating fully with authorities” and remain focused on safety and privacy.
Security experts note that high-profile media figures often face elevated risks due to public visibility. Threat assessments in such cases typically involve rapid verification of communications, digital forensics, and coordination with cybercrime units.

Law enforcement sources say forensic analysts traced metadata embedded in the alleged ransom messages. That analysis reportedly helped narrow down potential suspects within hours. Search warrants were executed shortly thereafter.
During the searches, authorities allegedly recovered electronic devices believed to be connected to the communications. Investigators are now conducting detailed examinations of those devices to determine intent, planning, and whether additional individuals were involved.
Officials stressed that, at this stage, the suspect is presumed innocent until proven guilty in court.
“This is a serious allegation,” the department spokesperson said. “But it is also an allegation. We urge the public to allow the judicial process to proceed without premature conclusions.”
The revelation of a suspect’s identity — though not yet publicly disclosed — has already sparked intense online speculation. Social media platforms lit up with theories and unverified claims within hours of the announcement, underscoring the challenges authorities face in high-profile investigations.
Legal analysts say that in cases involving alleged ransom or extortion plots, prosecutors must demonstrate intent, credibility of threat, and evidence that the suspect took meaningful steps toward carrying out the demand.
“If charges are filed, the prosecution will need to show more than just inflammatory messages,” one criminal law expert explained. “They must establish that the threat was actionable and that there was a deliberate effort to obtain money or leverage.”
Meanwhile, additional security measures have reportedly been implemented around the family as a precaution. Law enforcement officials declined to discuss specifics but confirmed that safety planning is ongoing.
The case also highlights the broader issue of digital anonymity and how quickly investigators can now trace electronic communications. Cybercrime units increasingly rely on IP tracking, device fingerprinting, and data preservation orders to identify suspects in cases involving threats or extortion.
Despite the tension surrounding the investigation, officials described the response as “measured and controlled.”
“There was no immediate physical confrontation,” one source noted. “The situation was contained through investigative means.”
As the investigation continues, authorities are expected to provide further updates once formal charges — if any — are filed. Until then, the focus remains on evidence review, interviews, and coordination with prosecutors.
For the public, the story serves as a reminder of the vulnerabilities that can accompany public life. For investigators, it represents a complex blend of digital forensics, legal standards, and careful communication.
What began as a disturbing alleged ransom message has evolved into a high-profile criminal investigation. With a suspect now identified and evidence under review, the next phase will unfold inside courtrooms rather than headlines.
Officials reiterate that this remains an active case — and that facts, not speculation, will determine its outcome.



Leave a Reply